Today, blocking websites is a frequent practice in corporations, governments, and educational institutions.
If you’ve encountered websites that have been blocked at your school or place of business, the management usually doesn’t want you accessing those websites using their ISP account — mostly to prevent you from falling down the rabbit hole.
They achieve this by blocking access to any of the websites on the blacklist for students and staff using firewalls that screen web content.
Thankfully, there are a few workarounds you can use to bypass a firewall at your school or place of employment and access the websites you want.
What Is a Firewall and How Does It Work?
A firewall is a hardware or software network security device that keeps track of incoming and outgoing traffic and blocks or permits particular traffic in accordance with complex security rules.
Firewalls are primarily used for access control, network traffic management, and control, resource defense, and recording or reporting of events, among other purposes.
Even while they protect all the machines on a specific network, they can be inconvenient, especially for students or staff who are unable to access their preferred social media sites, streaming services, or other websites.
Rarely do the users created on a computer in a school or place of business have administrative rights. As a result, you won’t be able to modify the firewall’s settings or take a website off the list.
However, if the firewall list is configured on the router, you will be subject to restrictions as long as you are connected to the network, regardless of what you do. This implies that even if you use a different device to test, the same regulations will still be in effect.
Although this is perceived as a problem, the good news is that there are solutions to this problem, which we will discuss in today’s article.
How to get past the school firewall:
1. To Get Around School Restrictions, Use a Proxy Site
2. Encrypt your traffic using a VPN
3. Try typing the IP Address of the Website
4. Use your smartphone as a mobile hotspot
5. Use Tor
1. Use a Proxy Site
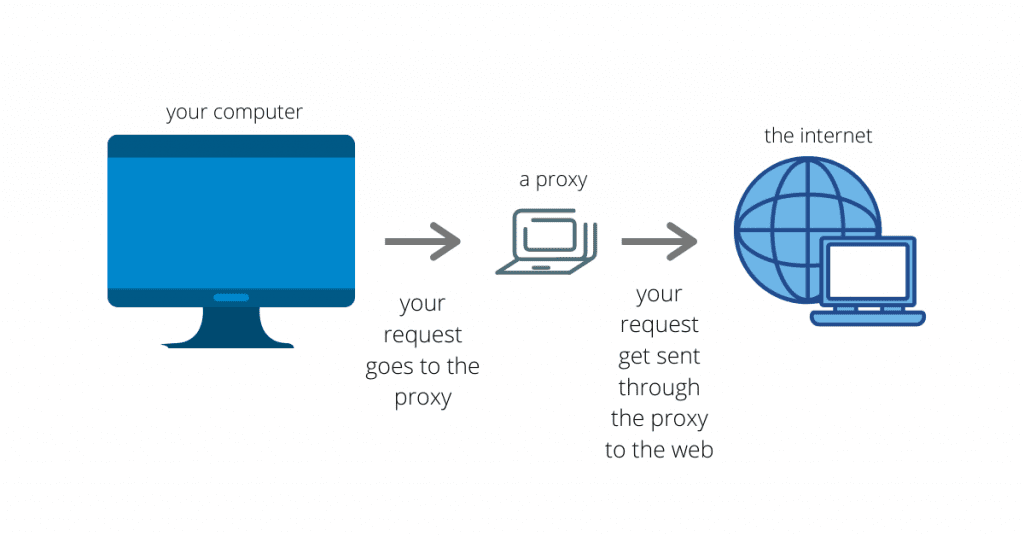
By handling all of your browsings for you, a proxy server can get past your school or workplace firewall and other URL restrictions. While the firewall only sees the proxy’s URL, it accomplishes this by visiting the website on your behalf and then displaying everything from it.
Although most proxies are free to use, they have significant disadvantages. You might not be able to access that website after all because they are unreliable, unsafe, and might leak your IP address.
Similarly, your school or workplace may also be using a proxy to block the websites as all requests have to go through it first.
Another drawback of this strategy is that occasionally the proxy site itself may be blocked. Unless you have one that’s not known to the management, it should probably work for you.
2. Using a VPN
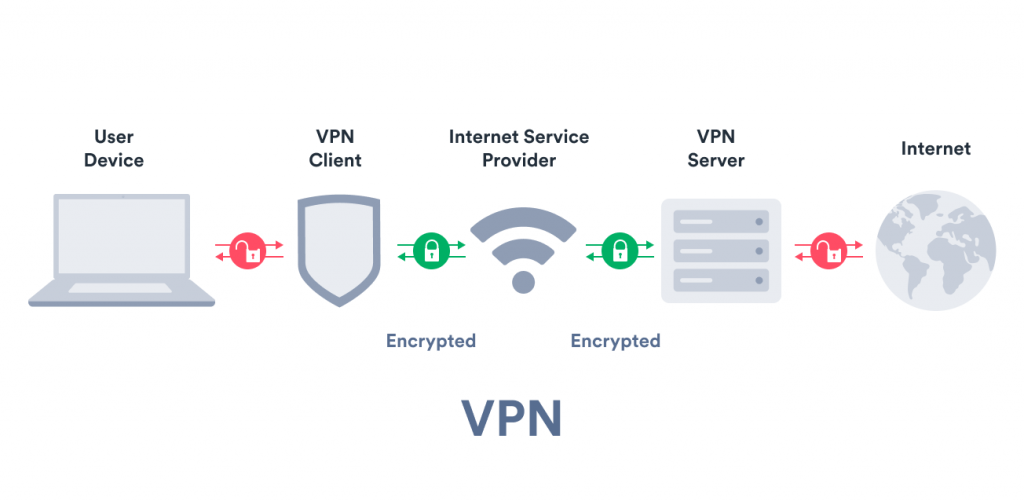
A virtual private network, or VPN, offers an encrypted and secure connection over the internet. Connecting to a server run by the service provider allows for this. Your true IP address will be concealed, and you will be able to access websites and materials that are banned.
VPNs are nodes on other computers that are linked to the internet that operates as a middleman to route traffic to the desired location. In this situation, a VPN has the modest advantage of establishing an encrypted tunnel through which data can pass. They are therefore a more secure solution because even if the traffic is intercepted, it won’t be useful to anyone.
The workings are the same when trying to get around a firewall restriction. The VPN routes the traffic in order to deceive the firewall into believing a different destination is the intended website server. You would be able to access websites that are ordinarily prohibited by doing this.
Since all VPN services cost money, there is a limited-use free alternative available. If this is a decent alternative for you, the built-in VPN in the Opera browser is not a bad choice to test.
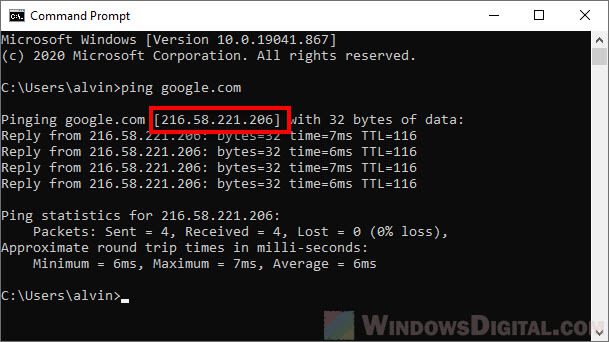
3. Use The Website’s IP Address
The easiest way is to use an IP address rather than a URL. There is something you should be aware of before you become very thrilled.
Some firewalls only block access based on the IP address while others do the same for the URL. When you enter a URL, the DNS locates the IP address connected to it and sends the information there.
You can test it out before you start to rely on it because this is a motorway. Enter the URL you want to view on a DNS lookup website.
You’ll receive an IP address as a result, which you should type into the address bar. You can proceed if you are able to access the website; otherwise, you will need to utilize a different approach.

4. Use your smartphone as a mobile hotspot
Make your smartphone into a mobile hotspot if utilizing a proxy or VPN sounds too complicated for you and you want a more obvious approach to browse your favorite websites without being “seen” on the school or business network.
You can access your favorite websites at any time in this way. Although it uses up your phone’s data, you can avoid the headaches of needing to go over firewalls and other internet restrictions. Additionally, it eliminates the risk of someone finding out what you are doing on the network at work or school.
Before switching to your phone’s internet connection and starting to use your content, be sure your cell provider permits tethering.
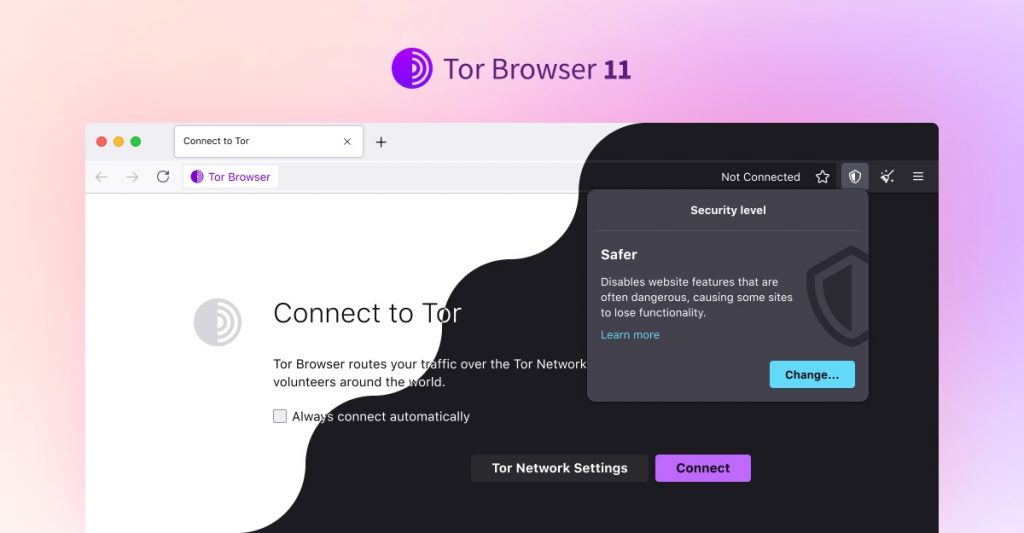
5. Use the Tor Browser
Popular web browser Tor enables anonymous browsing. Your web browsing is routed through an encrypted network before arriving at an endpoint that is perhaps unfiltered or blocked.
Although it allows you to circumvent your school or office firewall, it isn’t the ideal way to bypass firewalls compared to utilizing a VPN if you’re trying to access sensitive or unencrypted data.
It does, however, frequently function where proxies, common VPNs, or SSH tunnels fail, however it is substantially slower than ordinary online browsing.
School Proxy Bypass
Many schools block access to popular websites and social media platforms to prevent distractions and maintain a safe learning environment. However, this can be frustrating for students who need to access these sites for educational purposes or personal use during breaks.
Fortunately, there are several ways to bypass school firewalls and access blocked sites using proxy servers. A proxy server acts as an intermediary between your computer and the internet, allowing you to access websites that may be blocked by your school’s network.
Here are some methods on how to bypass school firewall using proxy servers:
- Web-based proxies: Web-based proxies are the simplest way to bypass school firewalls. Simply search for “web-based proxy” on your favorite search engine and choose one from the results. Enter the URL of the blocked site into the proxy server’s search bar, and the site will be loaded through the proxy server.
- Browser extensions: Many browser extensions can also be used as proxy servers. Install an extension like Hola or ZenMate and activate it when you need to access a blocked site.
- Virtual private networks (VPNs): VPNs are more secure than proxies and can be used to bypass school firewalls. VPNs encrypt your internet traffic and hide your IP address, making it difficult for your school’s network to detect your online activity. There are many VPN services available, both free and paid.
While these methods can be effective, it’s important to remember that bypassing school firewalls may be against school policies. Use these methods at your own risk and only for educational or legitimate purposes.
Should You Bypass Your School Or Workplace Firewall?
In addition to being caught in the act and maybe receiving a suspension, expulsion, or termination, breaking the rules as it were carries a number of other risks. Other consequences include having your private information stolen, contracting viruses that can spread to other computers in the classroom or business, or, even worse, being held accountable for your actions in court.
Firewalls are not set up to bother you; they are set up to keep you secure online. They are designed to help foster learning at school and increase efficiency at work. Before you attempt to circumvent the firewall barriers, decide if the risk is worthwhile in light of the stakes.
Conclusion
If you’ve encountered websites that have been blocked at your school or place of business, the management usually doesn’t want you accessing those websites. There are a few workarounds you can use to bypass a firewall at your school or place of employment.
To Get Around School firewall Restrictions, Use a Proxy Site, encrypt your traffic using a VPN, try typing the IP Address of the Website, use your smartphone as a mobile hotspot or Use the Tor web browser.
In addition to being caught in the act and maybe receiving a suspension, expulsion, or termination, breaking the rules as it were carries a number of other risks.
FAQ
Is It Illegal To Bypass A School Firewall?
Yes, you won’t run into any problems if you choose to get around the firewall legally. Once the firewall is bypassed, what you do is essential, because hostile actions are typically illegal.
That being said, there can be repercussions if someone from your school or workplace finds out.
How does a Firewall Blocks Websites?
A TCP packet containing an HTTP request, which is created whenever a machine wants to view a specific web page, is sent over the network. The TCP packet then proceeds to an IP layer for the routing procedure when the domain name of the website is converted to an IP address.
The layer decides which website server the request will be delivered to based on the IP address and routing tables.
The firewall acts at the IP layer and monitors each data packet using a “wall of code” to ban your device from the web at this point if the website is present on the network.
Why do schools block access to certain websites?
Schools block access to certain websites to prevent distractions, maintain a safe learning environment, and comply with legal requirements related to student safety and data privacy.
Can I get in trouble for bypassing school firewalls?
Yes, bypassing school firewalls may be against school policies and could result in disciplinary action. Use these methods at your own risk and only for educational or legitimate purposes.
What are web-based proxies?
Web-based proxies are websites that act as intermediaries between your computer and the internet, allowing you to access blocked websites. Simply enter the URL of the blocked site into the proxy server’s search bar, and the site will be loaded through the proxy server.
What are browser extensions?
Browser extensions are add-ons that can be installed on your web browser to add new features or functionality. Some extensions, such as Hola or ZenMate, can also be used as proxy servers to bypass school firewalls.
What are VPNs?
Virtual private networks (VPNs) are services that encrypt your internet traffic and hide your IP address, making it difficult for your school’s network to detect your online activity. VPNs can be used to bypass school firewalls, but it’s important to choose a reputable provider and use it responsibly.
Are there any risks associated with using proxy servers or VPNs?
Yes, using proxy servers or VPNs can introduce security risks and may slow down your internet connection. It’s important to choose a reputable provider and use it responsibly. Additionally, using these services may be against school policies and could result in disciplinary action.
How to bypass a firewall?
Bypassing a firewall is not an ethical or responsible action. Firewalls are designed to protect networks and systems from unauthorized access, security threats, and potentially malicious activities. Trying to bypass a firewall without proper authorization or legitimate reasons can have serious consequences and may be illegal.
Firewalls are implemented for a reason, and their purpose is to ensure the security and integrity of computer systems and networks. They help prevent unauthorized access, protect sensitive information, and mitigate potential risks.
If you are facing issues accessing certain websites or services due to a firewall, I recommend following these steps:
Contact the Network Administrator: If you are trying to access a specific website or service that is blocked by a firewall, reach out to the network administrator or IT department responsible for managing the network. Explain your situation and provide a legitimate reason for needing access. They may be able to help you or provide an alternative solution.
Use a Proxy Server or VPN: In some cases, if accessing certain websites or services is restricted based on your location or network, you can try using a proxy server or a Virtual Private Network (VPN). These tools can help mask your IP address and route your traffic through a different server, potentially bypassing certain firewall restrictions. However, keep in mind that using proxy servers or VPNs may not always be allowed or appropriate, depending on the network policies and regulations in place.
It’s important to remember that attempting to bypass firewalls or engage in any unauthorized activities can have legal and ethical implications. Always ensure that you have proper authorization and legitimate reasons before attempting to access blocked resources or circumvent security measures.

![How to bypass schools firewall that blocks most popular sites 1 How to bypass schools firewall that blocks most popular sites [2022]](https://speedtestgo.com/wp-content/uploads/2022/07/pexels-andrea-piacquadio-3799830.jpg)


